German researchers say they’ve found security gaps in four models of DJI drones – albeit not the kind that US politicians have claimed to justify placing the company’s craft on federal blacklists.
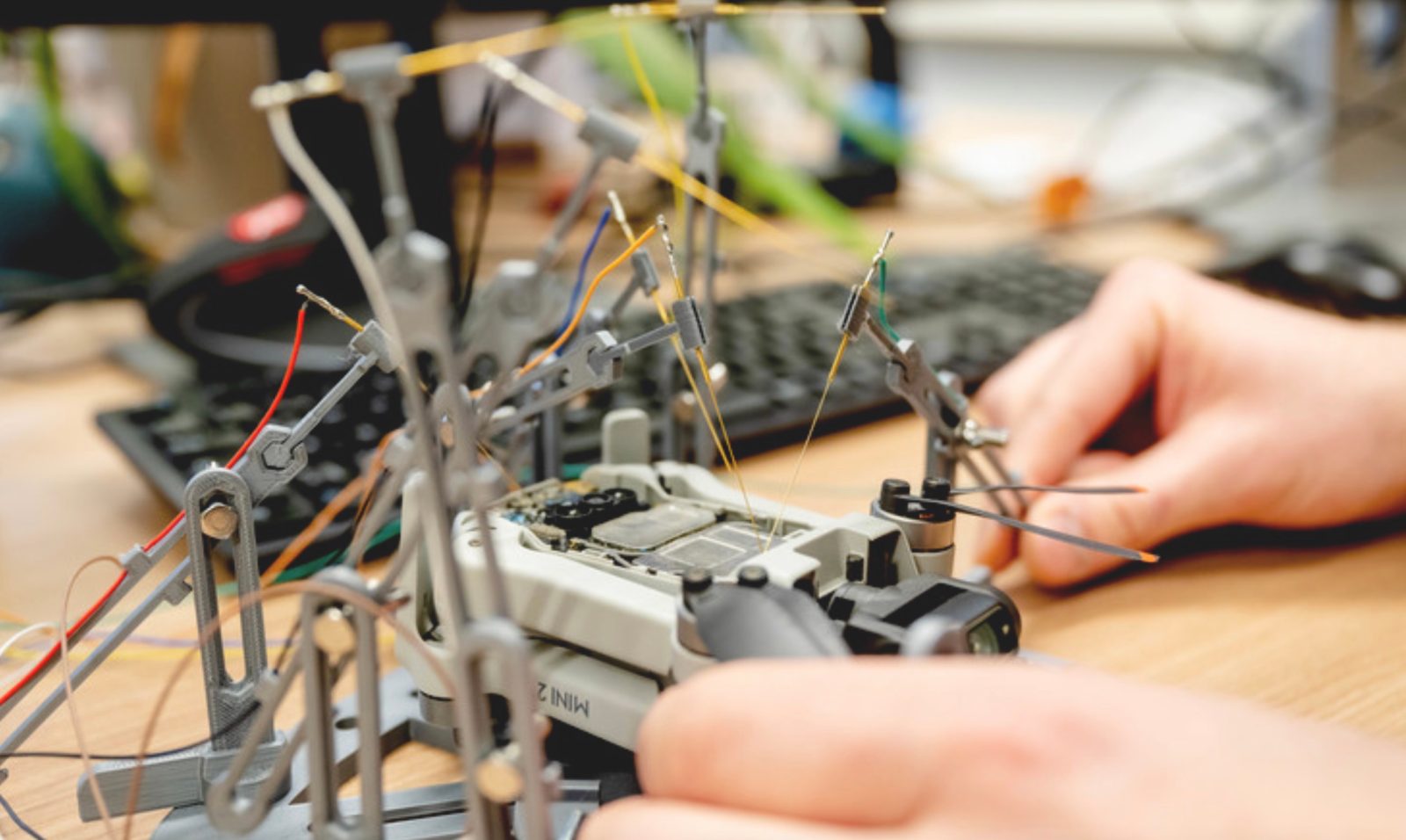
The team at the Horst Görtz Institute for IT Security at Ruhr University Bochum, Germany says its experiments allowed researchers to over-ride various security measures baked into the firmware of four models of DJI drones – one of which would allow third-party hackers to determine a pilot’s exact location. Other consequences include operators themselves altering UAV software to modify distinguishing information like the serial number, or otherwise prevent authorities from identifying the craft remotely.
DJI drones involved were DJI Mini 2, Mavic Air 2, Mavic 2, and Mavic 3.
While potentially troubling if exploited by hackers for nefarious ends, the security flaws found in those DJI drones were of an entirely different nature than those US officials have cited in placing the company’s products on blacklists. Typically, those have been based in large part on claims – thus far unsubstantiated – that the firm’s UAV operating systems allow private, potentially sensitive user data to be transmitted to authorities in China’s government for exploitation.
The Horst Görtz Institute findings, at least for now, are of another sort.
They indicate inadvertent firmware weaknesses that could be of use to hack-minded operators to mask their ID, or third parties seeking to locate pilot positions. Fliers of DJI drones in Ukraine, be warned: Another upshot of the research is the additional confirmation that DroneID information communicated by the company’s craft is not encrypted.
Read: DJI drones still flowing to Russia despite April suspension of sales [Report]
Unit leaders Nico Schiller and Thorsten Holz say they developed an algorithm to enable fuzzing used in the tests – a method by which the drone hardware and firmware were bombarded with random inputs streamed using the same DUML protocol as DJI craft. Researchers then determined which data packets caused the UAV OS to crash – and which resulted in alterations.
“Not all security gaps resulted in a crash,” says Holz. “Some errors led to changes in data such as the serial number.”
In addition to the study demonstrating how hackers could locate exact pilot (rather than drone) position, researchers discovered other ways forced firmware alterations modified UAV functions once outside parties gained access to the craft.
“An attacker can thus change log data or the serial number and disguise their identity,” explains Holz. “Plus, while DJI does take precautions to prevent drones from flying over airports or other restricted areas such as prisons, these mechanisms could also be overridden.”
The unit found a total of 16 security vulnerabilities, four of which are considered serious. All of those were communicated to DJI to allow the company to reinforce potential flaws on drones involved.
Meaning, rather than debunking US security allegations used to motivate blacklisting, the researchers instead have added to DJI’s workload to prove their craft are secure.
The full report on the Horst Görtz Institute work is available here.
Photo: RUB, Marquard
FTC: We use income earning auto affiliate links. More.




Comments